Ever wondered how secure your satellite insurance really is? What if a hacker could intercept your data mid-transmission, leaving you unprotected in the most critical moments? In this post, we’ll explore why Transmission Security Protocols matter for your satellite insurance and how they protect your assets. Spoiler: It’s not just about paperwork; it’s about protecting you from invisible threats.
Table of Contents
- Key Takeaways
- Why Satellite Insurance Is Vulnerable Without Security
- How Transmission Security Protocols Work
- Best Practices for Securing Satellite Insurance Data
- Real-Life Examples of Breaches and Wins
- Frequently Asked Questions (FAQs)
Key Takeaways
- Transmission Security Protocols safeguard sensitive satellite insurance data.
- Data breaches can lead to massive financial losses—protocols prevent them.
- Implementing encryption and authentication layers is non-negotiable.
- “DIY security” shortcuts are terrible ideas for high-value industries like satellite insurance.
- A proactive approach minimizes long-term risks.
Why Satellite Insurance Is Vulnerable Without Security
Satellites aren’t just floating hunks of metal—they’re invaluable for communication, weather tracking, agriculture, and national defense. If something goes wrong with one, having satellite insurance ensures stability. But here’s where things get dicey:
In my early days as an insurance nerd, I made a rookie mistake—I assumed satellite policies were untouchable because “space tech” had its own magical safeguards. Yeah, no. Hackers love targeting vulnerable systems, especially when companies ignore proper protocols. Remember the 2021 cyberattack on SpaceX’s Starlink network? That’s just one example of what happens when digital defenses fail.
Without robust Transmission Security Protocols, your satellite insurance provider might lose access to crucial policy details or worse—leave room for fraudsters to manipulate claims.
Figure 1: Visual representation of common cybersecurity gaps in satellite data transmissions.
—
How Transmission Security Protocols Work
So, how do these mysterious protocols actually keep your satellite insurance safe?
Step 1: Encryption
Imagine sending a letter wrapped in invisible ink—it’s gibberish until someone applies the right decoder. Encryption does exactly that but with computer algorithms. For satellite insurance, Advanced Encryption Standard (AES) locks down claim forms, policy details, and other sensitive exchanges.
Step 2: Authentication
Even if you send encrypted data, how do you ensure only authorized parties receive it? Enter Public Key Infrastructure (PKI). Each party gets verified credentials before accessing the info—a bit like checking IDs at an exclusive club.
Step 3: Integrity Checks
Hackers don’t always steal data; sometimes, they tamper with it. Integrity checks use cryptographic signatures to detect unauthorized changes. Think of it like smelling milk before pouring it into coffee—you catch spoilage fast.
Grumpy You: “Do I really need to care about all this tech jargon?”
Optimist You: “Yes, because ignoring these steps leaves money—and trust—on the table.”
—
Best Practices for Securing Satellite Insurance Data
Now that you understand the basics, let’s dive into practical tips:
- Adopt Multi-Layered Defense Strategies: Combine firewalls, intrusion detection systems, and endpoint protection.
- Train Employees Regularly: Human error accounts for 95% of breaches. Teach staff to spot phishing emails and avoid risky downloads.
- Prioritize Third-Party Vetting: Ensure vendors also meet stringent security standards.
- Stay Updated: Outdated software creates backdoors for attackers. Patch everything immediately!
- Rethink DIY Security Shortcuts: Yes, setting up quick fixes sounds appealing—but it makes you low-hanging fruit for hackers.
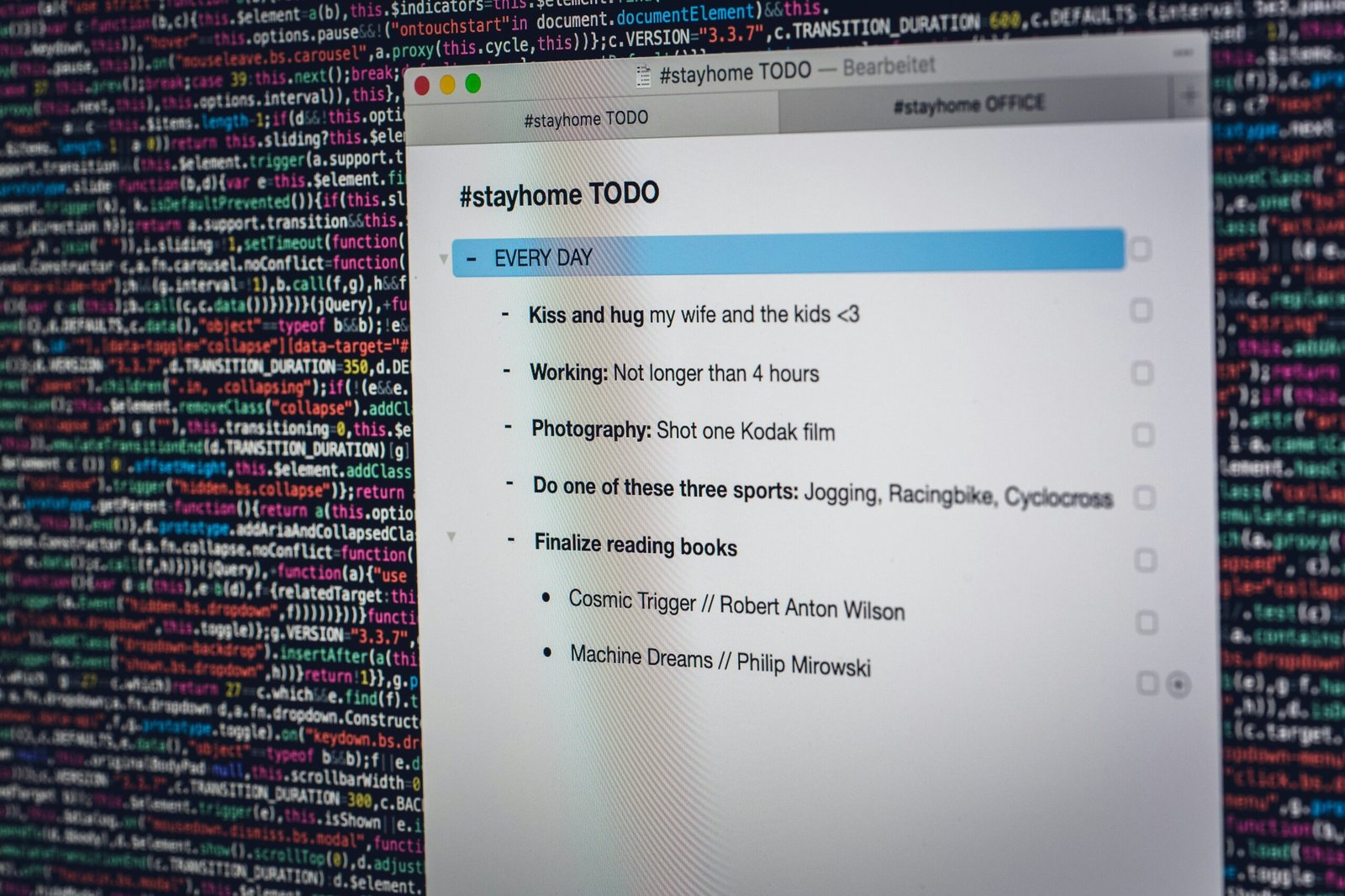
Figure 2: Common encryption tools used to fortify satellite insurance operations.
—
Real-Life Examples of Breaches and Wins
Let’s talk real-world scenarios. First, the disaster:
In 2018, a major insurer lost $5 million due to a man-in-the-middle attack during satellite deployment negotiations. Unencrypted emails allowed hackers to alter payment instructions undetected.
Now, the win:
One leading firm adopted Zero Trust Architecture combined with end-to-end encryption. Not only did they thwart multiple attempted breaches, but customer satisfaction scores soared too!

Figure 3: Impact of improved security measures over three years.
—
Frequently Asked Questions (FAQs)
What Are Transmission Security Protocols?
These are rules ensuring secure data transmission through encryption, authentication, and integrity verification.
Why Should I Care About Them for Satellite Insurance?
Because weak protocols put your coverage—and potentially billions—at risk of manipulation or theft.
Can Small Businesses Afford These Protocols?
Absolutely! Many affordable solutions exist, including open-source encryption tools tailored for small enterprises.
—
Conclusion
Satellite insurance isn’t just about protecting hardware—it’s about securing the flow of information surrounding those policies. With Transmission Security Protocols, you future-proof your investments against modern threats. Sure, it’s a hassle upfront—but skipping it is like driving without brakes.
And hey, remember childhood Tamagotchis? Just like keeping theirs alive required constant effort, staying ahead of cybercriminals demands daily vigilance.
“Securing satellites today means protecting tomorrow’s innovations.”